Telecom Fraud Prevention Tips
I recently read a New York Times (NYT) article on how a small architectural company left the office on Friday and came back on Monday to a $166,000 telephone phone bill from the weekend.
Sure. Likely story. But I read it through and found that there's a lot I don't know about today's telephone fraud.
It turns out that this customer was using Time Warner Cable for their POTS lines, connected to their phone system. The phone system (not Time Warner) was somehow hacked remotely so that incoming calls into their phone system over the weekend were forwarded to premium rate telephone numbers in Gambia, Somalia, and the Maldives.
Once the hacking to the phone system was finished, a computer made calls to the company, forwarded by the hacked phone system to the premium rate numbers through the whole weekend. Over, and over and over.
How is that possible? In the US we had local 976 calls and then national 900 calls where each call to that number racked up $1 to maybe $20 a minute. Whatever the 900-line provider thought they could get for what they were advertising (usually sex).
In the US 900 numbers were pretty much killed by the Internet where there's more sex to be found than anybody will ever be able to look at. Most US phone lines come with an option to block 900 number calls, which pretty much killed 900 numbers off.
Now the whole world is local. We can make a call to the Caribbean, Asia or Africa just like we can call next door, and it's usually only pennies a minute. Except when someone in a foreign country decides to setup a premium rate telephone number for maybe $20 a minute or more.
There is no blocking for international premium rate numbers by US phone companies. The phone numbers pretty much look like any other international call.
Phone companies handle the premium rate numbers by adding them to your bill as a separate line item, but the gist of the NYT article is that all phone companies are not the same!
Apparently larger phone companies have fraud detection built-into their systems so that it will prevent this kind of fraud. Smaller phone companies don't? So, the small seven man company with Time Warner Cable phone lines ended up with $166,000 worth of premium rate calls in one weekend.
Time Warner won't credit them for the fraudulent calls, telling the company that they have to pay these fraudulent charges.
Is there a way to know whether your phone lines or system can be hacked? Maybe not. Asking your phone line provider is probably a waste of time. You'd probably get a better answer from your pet turtle (you wouldn't get a wrong answer, anyway).
A better solution is to prevent your phone system from being hacked as much as possible, and if it is hacked to limit the amount of monetary damage that can be done.
They might block you from reading it if you are not a NY Times subscriber, but the entire NYT article is at:
After reading that horror story I immediately started thinking about our company's exposure. This is the third time I've rethought it since our SIP Trunks have been hacked once, and our testing/backup VoIP PBX hacked once. To the tune of about $600 total. Not terrible for the last six years.
We have a bunch of real POTS lines that are not connected to a VoIP phone system or DISA and have no way of being transferred or call forwarded except from someone sitting at a phone on our non-VoIP phone system. Or from a butt-set at our demarc (which runs underground to inside our building). Or from a butt-set at the AT&T terminal that feeds our demarc.
Our VoIP phone system is our secondary phone system mainly used for outbound calls. It uses SIP trunks. Both are definitely vulnerable to being hacked.
I'm writing this on a Sunday morning. Here are the last few lines from the log on our VoIP server a few moments ago:
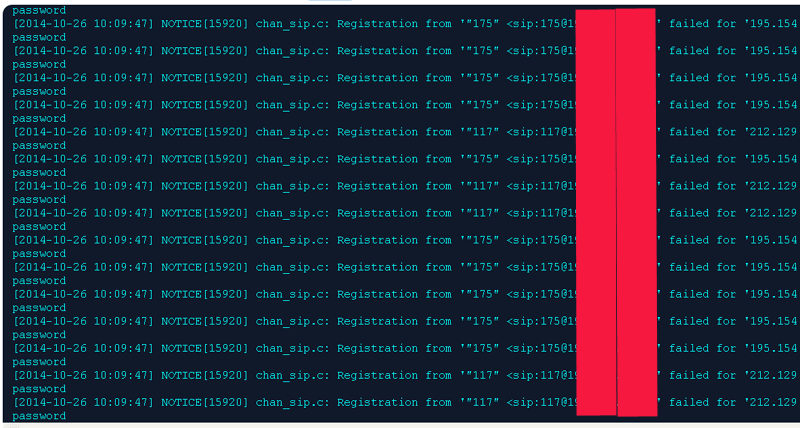
Within the same second there are dozens of attempts to hack into our VoIP system, to take over a station. It's all automated by the hackers and continues day and night. The hacker's IP address may be real or is more likely spoofed. There's probably no way to catch them, and none of the governments care. Reporting that your phone system has been hacked will be totally ignored by any police agency, anywhere. Your phone company will care even less if you actually end up having to pay them for the fraudulent charges.
So how do I prevent someone from eventually hacking our VoIP PBX or SIP trunks? I do the best I can but it's likely that we'll be hacked again. Here's how I mitigate the risk:
1. Keep the computer's OS and VoIP system updated on a regular basis (but not the same day patches or updates comes out!).
2. Remote access to the computer and VoIP system is whitelisted so it can only be administered from a couple of particular IP addresses.
3. Use good (secure) passwords for the VoIP stations and trunks. Don't allow anonymous SIP calls or SIP guests (every station must register to make or receive calls).
4. Run FAIL2BAN software (http://en.wikipedia.org/wiki/Fail2ban) which bans an incoming IP address for a while if there are too many password failures over a period of time from that IP. This will not prevent all hackers, but it's a good idea.
5. Block most countries (international calls) with our SIP trunk provider. Blocking all countries is usually the default, but our company does have to call out to some countries at times.
6. If your company really needs to dial into the "bad" countries you may be able to setup toll restriction in your PBX. Restricting every station from dialing 011 is a lot safer, but keep in mind that some countries with premium rate numbers may be reached with 1 and an area code (like 1-441 for Bermuda). Voicemail is available all night and on weekends for hackers to play with.
7. Use SIP trunks that are prepaid. Having an open account is handy at a company but it can lead to incredibly huge phone bills if your system is hacked (think $166,000!). Our SIP trunk provider sends me an email when our prepaid balance drops below maybe $100. I add $50 or so at a time with a credit card or PayPal when I get the email. When our system is eventually hacked again it will be a hassle to un-hack or restore it from a backup, but we'll only be out $100 or so. I figure it's just a cost of using VoIP and modern technology, but I'm limiting my exposure. Another company may be willing to limit their exposure to $500 or more? Even with an open account a phone line provider may be willing to limit credit to $500 or $1,000 before turning off the service?
There are so many bad guys trying to hack VoIP phones today that there's probably no way to keep them out.
VoIP phones are just plain easier to hack than computer servers at the average company. What will a guy in Russia do with the data off a particular small company's server (if it doesn't have credit card numbers)? Probably nothing. It's too hard to monetize a small company's data.
But if they can login to even one station, they can call forward that station to the premium rate international number where they may make $20 per call. And then start pumping hundreds or thousands of calls through until the company finds out - or the phone line / SIP trunk provider realizes they are fraudulent calls and blocks them.
If a company has call forwarding on the first line so that calls can be forwarded to a cell phone or home at night, and the call forwarding can't be changed remotely, they're pretty safe. It's only when call forwarding can be changed remotely that you're at a high risk.
One of the guys they interviewed for the NYT article, Jim Dalton from TransNexus, owns a company who sells fraud detecting software to phone companies. I think this article made it to the national stage to try to convince Time Warner to buy his software, but there are probably lots of other phone line providers who can't detect fraud. As users or even resellers, I don't know that there's any way for us to know which ones do detect fraud? Or what types of fraud will they detect?
I certainly wouldn't trust anything a phone company customer service rep told me over the phone!
All it takes is one VoIP station or a voice mail port on a non-VoIP phone system being hacked. It will then forward incoming calls to an international premium rate number. It can cost tens of thousands of dollars in hours.
The cost to the bad guy is almost nothing. Some time to manually hack into a phone or voicemail port (using default or common passwords), a cheap computer to search out VoIP stations to hack into ($100.00?), and a cheap computer to pump calls into the hacked extension that forwards calls to the international premium rate numbers ($100.00?).
There are tens of thousands of hackers doing this from countries all over the world, right this second. This is no joke.
 Products
Products